Agency for Cybersecurity
Making the world the safest place to live and work online
Find resources to help you or your organization to recover.
Structure around three strategic pillars ➔

Infrastructure Protection
• Presiding Firewall Architecture
• Network Detection & Response
• Endpoint Protection (AI Antivirus)
• Secure File Server Systems
• Video Surveillance Integration
• UPS / Power Continuity Systems

Identity, Access Governance & Control
• Enforced User Access Control
• VPN & Secure Remote Access
• Zero-Trust Access Models
• Enterprise Password Management
• Privilege Segmentation
• Continuous Access Monitoring

Business Continuity & Compliance
• Business Continuity Planning
• Disaster Recovery Architecture
• Orchestrated Backup Systems
• GDPR Compliance
• NIS2 Alignment
• Risk Assessment & Gap Analysis

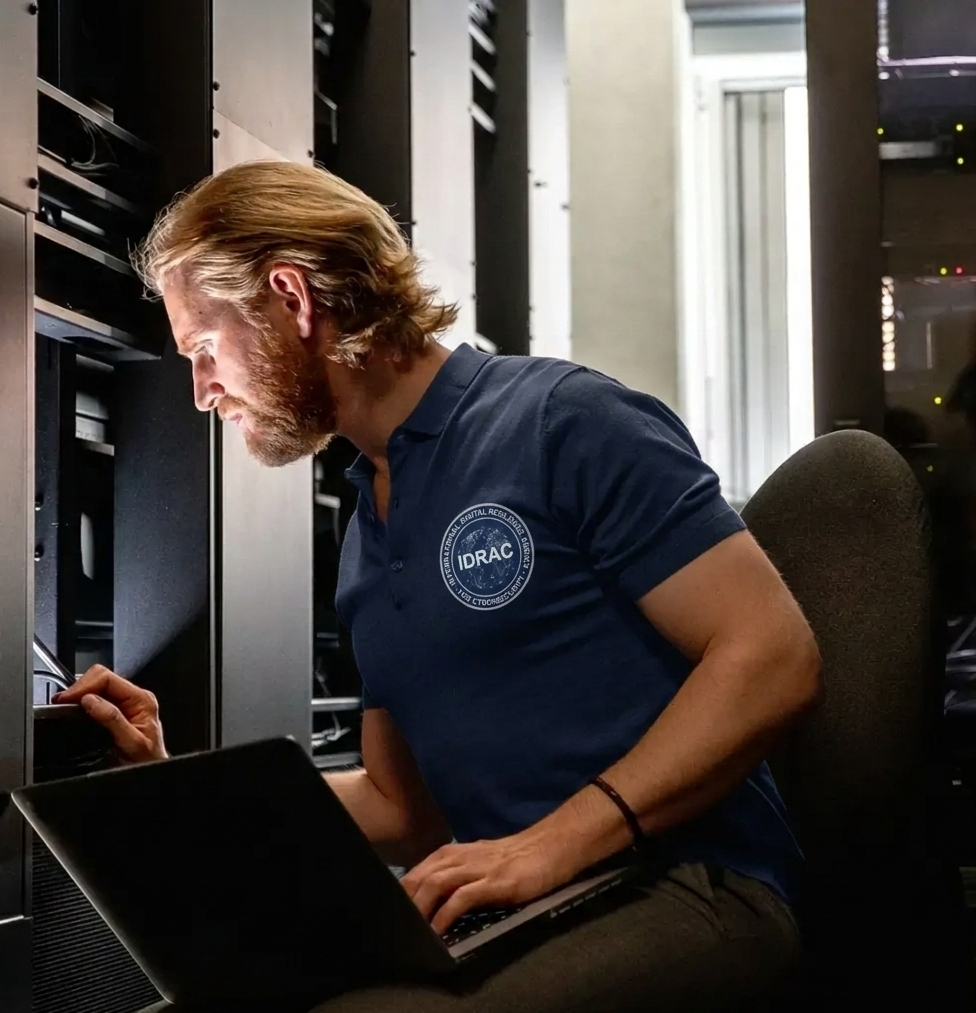
The vision behind IDRAC
IDRAC is dedicated to strengthening cyber resilience and safeguarding critical digital infrastructures.
The initiative is guided by Mirko Tozzi, a certified cybersecurity professional with over 15 years of experience in the protection, analysis, and governance of complex information systems.
“Business security is not a cost, it is a responsibility.”
Industry Applications ➔
Ensuring operational continuity and security across sectors
No protection against internal lateral threats.
IDRAC BCDR
Business continuity & Disaster Recovery
Critical operations remain available even in the presence of incidents, system failures, or cyber attacks. Structured procedures, resilient infrastructures, and rapid recovery capabilities allow organizations to maintain operational stability and restore essential services with minimal disruption.
Each Business Continuity and Disaster Recovery plan is tailor-made designed to anticipate potential threats, contain incidents, and maintain operational integrity, providing organizations with confidence in the resilience of their critical systems.
IDRAC NDR
Network Detection & Response
Exclusive patented technology for monitoring internal network activity and identifying anomalous behavior undetected by traditional security systems.
The system analyzes internal traffic and identifies lateral movement, privilege escalation, and suspicious activity, enabling immediate intervention before the incident spreads within the infrastructure.
Operational Capabilities
- International Industrial Patent (PCT)
- Patented Energy Air-Gap for immediate isolation of compromised network segments.
- Plug & Play installation with autonomous operation.
- Immutable logs recorded on blockchain for event integrity and auditability.
- Alignment with major security standards
NIST • ISO 9001 • ISO 27001 • NIS2 • GDPR
Operational Approach ➔
Threat Monitoring & Response
Operational Continuity & Resilience
Regulatory Alignment & Risk Governance
Short Heading for Testimonials Section Will be here


Build your resilience structure
Request an assessment
Understand your exposure.
Redesign your digital foundation.
